If there’s one organization you tend to trust with your information, it’s the government. The truth is though that many municipalities are simply not doing enough to protect themselves, and your data. Ransomware attacks are targeting municipalities due to their valuable information and security vulnerabilities.
Canadians and American Municipalities Both Affected
The following are some of the Canadian cities that have had cyber attacks occur since 2018:
- Cambridge, ON, CAN
- Stratford, ON, CAN
- Wasaga Beach, ON, CAN
- Midland, ON, CAN
- Regina, SK, CAN
- Mekinac, QC, CAN
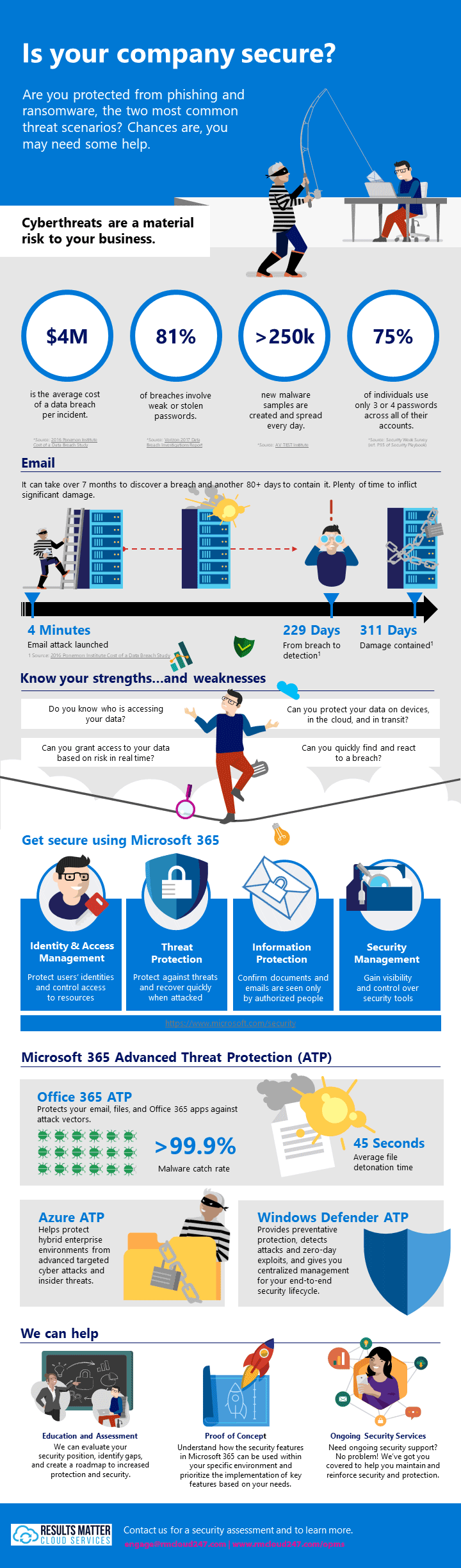
Recorded Future Blog compiled a list of American cities and public services hit by ransomware starting in 2013. The image below shows 2018 onwards, which is almost half of the list.

Almost half of the ransomware attacks on US cities since 2013 have occurred in the past year and a half.
More Than Pennies
On May 7, 2019, the City of Baltimore, MD was attacked for the second time in 15 months. This resulted in disruptions to the city systems for over 2 weeks. The expected cost of the attack to Baltimore is $18.2M. The city now looks to rebuild their systems and make up for lost revenue. It is not hard to imagine that Canadian municipalities are also at increased risk for ransomware attacks.
Are You Prepared for the Consequences?
As a small business owner, or member of government, how long are you willing to allow your systems to be down for, and how much money are you prepared to lose? Have you considered the money lost during the time the business is down? The money required to rebuild critical systems? Ransomware attacks are becoming increasingly creative, and cities need to consider that any of the following could happen to them:
- Locking out of city employees from email accounts
- Locking out of city employees from phone systems
- Shutdown of 911 system
- Loss of police footage potentially affecting future cases
- Inability to complete real estate transactions
- Inability to pay parking tickets, taxes
Some Cities Are Stepping Up
In light of all of this, municipalities such as Fredericton, NB have taken steps to protect themselves by partnering with local companies to improve their cyber security and business continuity plans before a crippling cyberattack occurs. In this case, Fredericton approved spending of upwards of $100,000 per year for 3 years. With proper preparation, municipalities can better protect themselves and their citizens, and limit their damages and downtime in the event of an attack.